Using public Wi-Fi hotspots can be incredibly convenient, whether you’re traveling or just working from a local coffee shop. However, these networks are often not very secure and can become targets for cybercriminals.
These malicious actors might attempt to steal your data, direct you to scam websites, and load your devices with harmful software. The only way to protect yourself is to use the best VPN for Wi-Fi.
The best VPN encrypts your internet traffic through a secure, private tunnel. It also conceals your IP address, rendering your online actions hidden and unreachable by potential hackers. But with so many VPNs on the market, all claiming to offer superior protection, it can be hard to know which ones deliver.
After extensively testing numerous VPN services and examining their encryption methods, security features, and tunneling protocols, I’ve identified the top VPNs for ensuring robust protection on public Wi-Fi networks in 2024.
My top recommendation for staying shielded against these threats is ExpressVPN, which not only offers robust encryption but also boasts a proven track record of protecting privacy. However, it’s not the sole option. For more information, keep on reading!
Quick Overview: Best VPN for Wi-Fi
Here is a list of the best VPN for Wi-Fi in 2024:
Why Do I Need a VPN for Wi-Fi?
Using a VPN for Wi-Fi is crucial to safeguard your online privacy, especially in public places. Public Wi-Fi networks are vulnerable to cyber snooping, which can expose your online activities. Whether on your computer or mobile device, a VPN ensures your data remains secure and private when connected to public Wi-Fi.
Here are some other reasons why you’ll need a VPN:
- Protects you from cyber threats: A VPN can efficiently hide your browsing data and any other activities across the web so that cyber criminals don’t get their hands on your data. They can anonymize your IP address and keep you safe from actors.
- Secures sensitive information: Using a VPN will ensure your confidential data, i.e., login credentials, banking information, personal data, etc., is safe. It’ll encrypt your data to ensure no third party can access it.
- Secures you while working remotely: Once a hacker gains access to your device, there’s a possibility they may hack your company as well. Using a VPN can help in preventing such cyberattacks and their consequences.
5 Best VPNs for Wi-Fi in 2024 [Detailed Analysis]
I tested 50+ VPN services based on security, encryption, servers, speeds, device compatibility, and more. Out of these, I shortlisted 5 VPNs that worked great on Wi-Fi:
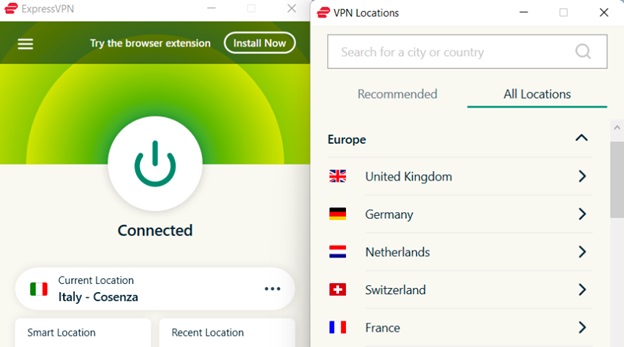
1. ExpressVPN – Best VPN for Wi-Fi

ExpressVPN is the best VPN for Wi-Fi as it offers a large server network that operates at consistently fast speeds. It is packed with advanced security features. These include an AES 256-bit encryption, keeping all your sensitive data secure even if a cybercriminal compromises your Wi-Fi connection. Its no-logs policy itself ensures not to collect any user data.
Good quality encryption is essential for public Wi-Fi since they are notoriously vulnerable to hackers and security threats. As such, ExpressVPN offers the best protocols, including IKEv2, OpenVPN, and Lightway. And being headquartered in the British Virgin Islands means it won’t be prying into your connection as it’s not a member of the 5 and 14 Eyes alliance.
Moreover, the ExpressVPN Threat Manager enhances Wi-Fi security. It identifies and blocks potential threats, providing an added layer of protection while using Wi-Fi networks.
ExpressVPN stands out not only for its security features but also for its vast server network of 3000+ servers in 105 countries. Optimized for speed, the server network is unrivaled in its ability to bypass geo-restriction, especially streaming platforms like HBO Max, Hulu, Amazon Prime, etc.
That’s right, by using ExpressVPN on Netflix, you can gain access to the platform’s vast international libraries full of binge-worthy shows.
My ExpressVPN speed test on a 100 Mbps connection did not disappoint. I got a blazing-fast download speed of 89.64 Mbps and an upload speed of 84.64 Mbps.
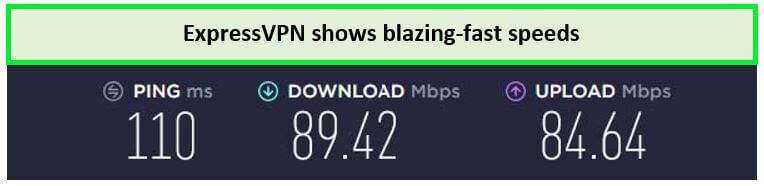
This speed is enough to download P2P files within seconds.
The VPN connects up to 8devices on a single subscription. It also comes with 24/7 live chat support in case you face any issues, including inquiries about the ExpressVPN cost.
For more information, check out my ExpressVPN review.
Exclusive Deal
VPNRanks readers can enjoy a special ExpressVPN offer! $3.99/mo - Save up to 63% with exclusive 2-year plan + 3 months free
Pros
- RAM-only servers
- Audited no-logs policy
- Obfuscated servers
- Threat Manager included
- Industry-leading encryption
Cons
- Discount campaigns end too soon
2. Surfshark – Affordable VPN for Wi-Fi

Surfshark is the most affordable VPN for Wi-Fi. The VPN comes at a super-affordable price and offers a great service.
Headquartered in the Netherlands, Surfshark guarantees zero logs. This ensures that the VPN won’t collect any user data itself. Not only that, but Surfshark also offers industry benchmark protocols and security features like a kill Switch, AES 256-bit encryption, and even an ad-blocker to block trackers on Wi-Fi networks.
The VPN also comes with a Whitelister feature that lets you decide which apps or websites you want to route through the VPN-enabled connection and otherwise. Let’s not forget that Surfshark is one of the few VPNs that come with the latest WireGuard protocol that offers fantastic speed and security.
Surfshark servers list consists of 3200+ servers in 100 countries, which helps you unblock multiple geo-restricted sites, including streaming services like Netflix, Hulu, Max, Amazon Prime, etc.
I tested Surfshark with Netflix and was surprised to see that the VPN allowed me access to its international libraries without compromising the video quality.
My Surfshark speed test revealed that it could achieve an extremely fast download speed of 81.32 Mbps and an upload speed of 76.12 Mbps on a 100 Mbps connection.

I achieved blazing-fast speed results
Find out more about the qualities of this service in my Surfshark review.
Exclusive Deal
VPNRanks readers can enjoy a special Surfshark offer! $2.49/mo - Save up to 77% with exclusive 2-year plan + 30-day money-back guarantee
Pros
- Best Android VPN for Wi-Fi
- Budget-friendly pricing plans
- Effective kill switch
- Comes with an Antivirus
- Unlimited simultaneous connections
Cons
- Apple client apps need improvement
3. NordVPN – Secure VPN for Wi-Fi

NordVPN is, without a doubt, the most secure VPN for Wi-Fi. This VPN comes with a variety of advanced security features along with a massive server network of 6000+ servers, perfectly capable of securing users on Wi-Fi.
NordVPN’s security features include DoubleVPN, which protects your online security even when connected to Wi-Fi. It further comes with obfuscation technology that doesn’t let your ISP know you’re using a VPN on your connection.
It is also one of the best VPNs to deter snoopers and cyber-criminals, thanks to its powerful 256-bit encryption. Its kill switch and no-logs policy are also pretty effective regarding privacy and online protection.
NordVPN’s server list consists of 6000+ servers in 61 countries, delivering high-speed and encrypted connections. This diverse server network provides users with anonymity online and the ability to access content on BBC iPlayer, Hulu, and Netflix with NordVPN.
The speed test for NordVPN indicates how fast this VPN can perform. On a 100 Mbps connection, it delivered an impressive download speed of 83.82 Mbps and an upload speed of 44.64 Mbps.
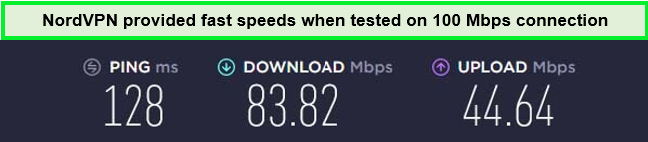
NordVPN proved to be a true streaming VPN by delivering fast-speed results during my test.
For more information, check out my NordVPN review.
Exclusive Deal
VPNRanks readers can enjoy a special NordVPN offer!$3.99/mo - Save up to 63% with exclusive 2-year plan + 3 months free
Pros
- Best VPN Wi-Fi encryption for mobile phones
- Huge server network
- 6 simultaneous connections
- Threat Protection
- Audited no-logs policy
Cons
- No app for routers
- Windows app takes up too much screen space
4. IPVanish – Fastest VPN for Wi-Fi

IPVanish is the fastest VPN to use on your Wi-Fi connection. The VPN will guard your online privacy and activity when on Wi-Fi, offering great speeds to give you a lag-free browsing experience.
IPVanish further comes with amazing security to stay away from all cybercriminals. It has the strongest 256-bit encryption to keep your online activity safe. It also offers you a dedicated IP and allows you to torrent anonymously.
This VPN also comes with split tunneling that lets you split your traffic between a VPN-enabled connection and your normal one. Although based in the US, a member of the 5 Eyes, this VPN comes with a strict no-logs policy that ensures your data remains protected from prying eyes.
IPVanish offers 2200+ servers in countries for bypassing geographical blocks. To check its unblocking, I connected IPVanish with Netflix and was delighted by the results.
Upon conducting the IPVanish speed test on a 100 Mbps connection, I achieved a download speed of 86.75 Mbps and an upload speed of 73.67 Mbps, and there were no buffering issues.
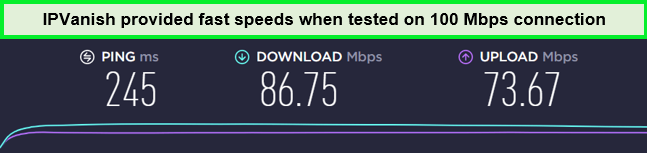
No significant speed drop was recorded during IPVanish speed testing.
Check out my detailed IPVanish review for more information.
Exclusive Deal
VPNRanks readers can enjoy a special NordVPN offer! $2.99/mo - Get 3 Months Extra + Save 77% on 2-year plan
Pros
- SOCKS5 proxy
- Securely access Netflix and similar services
- Unlimited device connections
- No-logs policy for privacy protection
Cons
- Based in the US
- No Bitcoin/cryptocurrency payment option
- Lacks browser extensions
5. CyberGhost – User-friendly VPN for Wi-Fi

CyberGhost is the most user-friendly VPN for Wi-Fi and its enabled devices. Browsing and streaming with CyberGhost is the easiest thing to do, as it offers optimized servers for all online activities.
CyberGhost also offers 11651+ servers and powerful encryption to help you stay safe on Wi-Fi. Not only that, but CyberGhost also offers powerful protocols like WireGuard, OpenVPN, SSTP, PPTP, IKEv2, and even L2TP.
It has a DNS leak protection feature that ensures your IP address doesn’t leak to any website or authority. It creates an encrypted tunnel between the connection and websites you visit so no third party can snoop in at any time. Furthermore, CyberGhost is based in Romania, a country safe from all data retention laws, which is a plus.
CyberGhost is a fantastic VPN service with an ever-expanding network of 11651+ servers in 100 countries. With unlimited bandwidth and traffic, it’s perfect for browsing, streaming, or torrenting on public Wi-Fi hotspots.
On my CyberGhost speed tests, I received a download speed of 75.47 Mbps and an upload speed of 69.34 Mbps on my 100 Mbps internet connection.
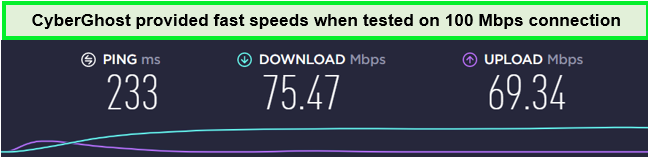
Enjoy decent streaming speed using CyberGhost’s servers.
Find out more about the qualities of this service in my CyberGhost review.
Exclusive Deal
VPNRanks readers can enjoy a special NordVPN offer! $2.03/mo - Save up to 84% with exclusive 2-year plans + 4 months free
Pros
- Fast-speed servers for quick connectivity
- Strong encryption and a no-logs policy
- 7 multi-device connections
- Includes 24/7 live chat support
- 45-day money-back guarantee
Cons
- Doesn’t work in China or the UAENor
- Not recommended for advanced users
Comparison Table: Best VPN for Wi-Fi
Compare the top VPNs for Wi-Fi with my quick comparison table. At a glance, you can evaluate features, pricing, server count, and more, making it easier to choose the VPN that fits your needs:
| VPNs |  |
 |
 |
 |
 |
|---|---|---|---|---|---|
| Ranking | 1 | 2 | 3 | 4 | 5 |
| Encryption Standards | AES-256 | AES-256 | AES-256 | AES-256 | AES-256 |
| No-Logs Policy | Strict | Strict | Strict | Strict | Strict |
| Streaming Sites | Netflix, Hulu, HBO Max, and more | Netflix, BBC iPlayer, Hulu, and more | Netflix, Paramount+, Crunchyroll, and more | BBC iPlayer, HBO Max, Hulu, and more | Netflix, Amazon Prime, HBO Max, and more |
| Supported Devices | Windows, Mac, Android, Linux, iOS, Routers, Smart TVs | Windows, Mac, Android, iOS, Linux | Windows, Mac, iOS, Android, Linux | Windows, Mac, iOS, Android, Linux | Windows, Mac, Linux, iOS, Android |
| Simultaneous Connections | 8 | Unlimited | 6 | 10 | 7 |
| Download Speed | 89.42 Mbps | 81.32 Mbps | 83.82 Mbps | 86.75 Mbps | 79.42 Mbps |
| Best Deal | $6.67/mo | $2.49/mo | $4.89/mo | $2.99/mo | $2.99/mo |
How I Selected the Best VPN for Wi-Fi in 2024
Given the vast variety of VPN options available in the market, choosing the best VPNs for public Wi-Fi can be quite challenging. However, security should be the foremost concern. With this in mind, I took into account several key factors while selecting these VPNs:
- Encryption: The encryption used by a VPN is crucial in ensuring the security of your data against hackers and third parties. Therefore, I have specifically selected providers that offer top-tier and unbreakable AES encryption.
- Security features: A VPN’s security is enhanced by the availability of supplementary features. For instance, a kill switch, traffic obfuscation, and threat detection, which further safeguard your online activities.
- Speed: I have selected providers that offer solid speeds, ensuring that the VPN service does not noticeably affect the performance of your device or disrupt your work.
- No-logs policy: I have exclusively chosen reputable VPNs that have a strict no-logs policy. Your data will not be stored or shared with third parties. You can rest assured that your information remains confidential.
- Supported platforms: I have ensured that the recommended VPN providers support at least four major platforms: Windows, macOS, iOS, and Android. This ensures compatibility and seamless protection across a range of devices.
- Simultaneous connections: To maximize the value of your investment in a VPN service, I have chosen providers that allow you to protect multiple devices with a single subscription. This feature enables you to secure all your devices without additional subscriptions.
- Pricing: I’ve only picked out VPNs that offer value for money. I wouldn’t want you to break the bank while opting for a VPN for your security. If you opt for the annual pricing plans, you’ll be investing in the long run and won’t have to renew your subscription every month.
The Risks of Using a Wi-Fi
Engaging in everyday online activities may seem harmless, but when connected to Wi-Fi, it can quickly become a risky endeavor. Here are some of the dangers associated with using public networks:
- Information theft: When connected to a public Wi-Fi network, cybercriminals can intercept the communication between you and the websites or services you access. This interception allows them to potentially read and steal sensitive information such as passwords, credit card details, or personal data.
- Malware infiltration: Hackers actively search for vulnerabilities in devices connected to public networks. Once they identify a vulnerability, they can exploit it to distribute malware to your device. This malware can lead to various malicious activities, including data theft, unauthorized access, or complete device control.
- Business-wide attacks: If you frequently work in public spaces and rely on public Wi-Fi, using these networks can pose a significant risk to your organization. An attacker targeting the public network could potentially gain access to your business network, leading to a company-wide breach, compromising sensitive data, and causing severe damage.
- Redirection to untrusted websites: Hackers may employ tactics such as DNS spoofing or malicious redirects to direct you to untrusted websites that lack secure protocols. These deceptive websites aim to trick you into revealing sensitive information, such as login credentials or financial details.
To mitigate these risks, it is essential to use a VPN (Virtual Private Network) when connecting to Wi-Fi. The best VPN for Wi-Fi security encrypts your internet traffic, ensuring that your data remains secure and inaccessible to prying eyes.
Additional Methods to Ensure Your Safety While Utilizing Public Wi-Fi Hotspots
When using public Wi-Fi hotspots, it’s important to take steps to ensure your online security:
- Double-check the name of the network you’re connecting to, as hackers often use fake networks with similar names to legitimate ones.
- Avoid using public Wi-Fi hotspots for sensitive tasks like online banking or purchasing. If you need passwords, consider using a password manager for added safety.
- Look for HTTPS and SSL in the address bar when connecting to websites. This means your connection to the website is secure and encrypted, making it much harder for anyone to intercept your data.
- Stick to networks that require passwords, such as those in cafes or hotels. This is much safer than connecting to a completely open public Wi-Fi hotspot.
- Disable automatic Wi-Fi connections on your phone to ensure you only connect to secure networks. You can set your device to ask before connecting to a network for added security.
How Does a VPN Protect You on Wi-Fi?
A VPN (Virtual Private Network) safeguards your online presence using Wi-Fi through data encryption. Essentially, your activities and personal information traverse through an encrypted tunnel, rendering them indecipherable to third parties such as governments, ISPs, or cybercriminals.
Additionally, a VPN masks your true IP address. When you connect to a VPN server, the IP address visible to others is that of the server itself. Moreover, certain VPNs offer the option to enable LAN invisibility, ensuring your device remains hidden from other users connected to the public network.
How to Set Up a VPN for a Wi-Fi?
You can set up a VPN for Wi-Fi by following the steps given below:
- Subscribe to a trustworthy VPN. I highly recommend ExpressVPN.
- Download and install the app on your device.
- Launch the app and sign in.
- Click on any server you want to connect to.
- Enjoy a safe and secure Wi-Fi connection!
Tips for Staying Safe on Wi-Fi Networks
Enhancing your protection on Wi-Fi networks requires more than just relying on a VPN. It’s essential to be aware of potential threats and take proactive measures. Here are some tips to ensure comprehensive protection:
- Disable auto-connect: Prevent your devices from automatically connecting to Wi-Fi networks. By doing so, you minimize the risk of unknowingly connecting to a malicious network, as hackers can position themselves between you and the Wi-Fi connection.
- Avoid typing sensitive information: Public Wi-Fi networks often lack robust security measures, making it easier for hackers to intercept and access your sensitive information, such as passwords or banking details. It’s advisable to refrain from entering such information while connected to public Wi-Fi.
- Visit secure websites only: Hackers can redirect you to fraudulent websites, compromising your data. To mitigate this risk, ensure you only access websites with secure protocols (HTTPS) that encrypt your communications and protect your information.
- Be cautious of shoulder surfing: When using your devices in public spaces, be mindful of your surroundings. Cybercriminals may attempt to peek at your screen and gather sensitive information while you’re typing. Stay vigilant and shield your screen to protect your privacy.
- Practice good password hygiene: Use a password generator to create strong and unique passwords for each website or service. To manage multiple passwords securely, employing a password manager is highly recommended.
- Enable two-factor authentication: Adding an extra layer of security by enabling two-factor authentication makes it significantly harder for cybercriminals to gain unauthorized access to your accounts. Without the additional authentication method, they cannot bypass this added protection.
- Set the Wi-Fi network to “Public”: To minimize your visibility on the public network, adjust your device’s Wi-Fi settings to categorize the network as “Public.” Additionally, on Windows devices, take advantage of the “disable device discoverability” feature, further limiting your exposure to other devices on the network.
By implementing these precautions, alongside utilizing a VPN, you can significantly enhance your security and protect yourself from potential threats while using Wi-Fi networks.
Top VPNs for Wi-Fi on Android
If you are a user of Android devices, you should always connect to the Wi-Fi through a VPN. Public Wi-Fi is especially vulnerable, as they usually have only basic encryption. As a result, any traffic that passes through the public Wi-Fi from your Android device is at risk of interception by authorities or hackers.
To ensure your safety online while using Wi-Fi on an Android device, you should always use a VPN service. The VPN providers reviewed above are compatible with Android OS and use the most advanced encryption protocols. Particularly, ExpressVPN is known for its state-of-the-art encryption standards.
Good encryption standards include protocols such as OpenVPN and IKEv2 (for mobile devices). On the other hand, encryption techniques like PPTP have become obsolete, as they are highly insecure forms of encryption. It is important to consider which encryption protocols are supported by a VPN provider before deciding to purchase one for your Android device.
Therefore, you should use ExpressVPN or other alternatives listed above to gain safe and secure access to public Wi-Fi on your Android. The kinds of malware and security threats that target Android devices are increasing with time. Purchasing a well-encrypted and reliable VPN is thus a worthwhile investment if you want to protect your Android device.
You can read my guide on the best encrypted VPN services to learn more about modern encryption algorithms that offer the best security.
Best Free VPN for Wi-Fi
The VPN industry consists of a large number of VPN providers. However, there are only a few providers that offer VPN services for free. Those VPN companies that do offer free versions do so in the form of watered-down software with several limitations.
For instance, most free VPN services offer limited bandwidth and only a few server options. In addition, they also have unsatisfactory logging policies and usually record user data. This information is then sold to advertisement companies for a profit. Since free VPN providers must make money to fund their operations, they use these tactics to make revenue.
Therefore, using a free Wi-Fi VPN for Android and most devices is generally a bad idea. I strongly recommend using paid VPN services to ensure security and encrypt your data. Nonetheless, there are a select few free VPN providers that do offer good VPN features.
ProtonVPN is one of the best free VPNs for Public Wi-Fi services that is worth a try. This VPN provider is unique since it is the only one that provides unlimited bandwidth with no caps. Moreover, it uses the most advanced robust security protocols, such as OpenVPN, to encrypt your data passing through the Wi-Fi network. Thus, ProtonVPN is the best free Wi-Fi VPN for Android you can acquire for free.
You can also protect your VPN Wi-Fi Password network through a VPN-based router. Read my guide on the VPN router for more information.
What is Publicly Available Wi-Fi?
Publicly available Wi-Fi is located in public places where people can easily access the internet. You encounter public Wi-Fi in your daily life when visiting public places. Due to the nature of this Wi-Fi, many people access the internet.
Where is this Wi-Fi available?
The most common places where these Wi-Fi can be found include:
- Restaurants, café, coffee shops
- For airports, subways, and trains, ProtonVPN is one free VPN service that is worth a try. This VPN provider is unique since it is the only VPN service that provides unlimited bandwidth with no caps. Moreover, it uses the most advanced.
- Hotels and hostels (Use the best VPN for hotel Wi-Fi to stay safe)
- Tourist places
- Malls, etc.
Whenever any Wi-Fi is easily accessible to anyone and is located in a public place, it is said to be public Wi-Fi. The reason why the internet is available to the public for free is so that their customers would spend extra time at their restaurants or shops. Extra time means more sales for shops.
Why Public Wi-Fi is Insecure?
Public Wi-Fi networks are insecure because it doesn’t require you to enter a password for their access. These are unencrypted connections, which means snoopers and cybercriminals can gain access to anyone’s device who is using Wi-Fi at the time. These snoopers can access your accounts, credit card information, pictures, and videos.
Other than your phone being hacked by snoopers, there is another possibility that you will become a victim of a man-in-the-middle attack. Snoopers can intercept the data being transferred from one device to another and eavesdrop on your communication.
Malware is easily injected by hackers onto your devices, which means everything you do on your device is easily recorded. Lastly, fake hotspots or Wi-Fi are created to tempt users to access them. As a result, malware is injected, and users are most likely to hack your phone. That’s why using the best VPN for public Wi-Fi per Reddit is necessary.
What Information is at Stake?
As I have made you aware of why public Wi-Fi is insecure, there is another thing that you need to be aware of. You must know which information is likely to get affected when snoopers try to inject malware or get access to your device. These are listed below:
- Location of your home
- Bank account details
- Internet history
- Pictures and videos
- Files and apps
- List of phone contacts
- Communication with friends
- Passwords, etc.
All the above information is easy to access once a hacker gets hold of your device within public Wi-Fi. Many cases emerge in tourist attractions and when boarding airplanes. In both situations, you are desperate to use the internet and require a Wi-Fi connection.
Secure your Information from Being Stolen on a Public Wi-Fi
There are several ways to protect your online data and device while using a Wi-Fi network, but a Wi-Fi VPN stands at the top of the league. It encrypts your online data, as does your IP, which means no users on the particular Wi-Fi network will ever know you’re using the same network.
When connecting to a VPN, not only snoopers or hackers would be able to know that you exist over the Wi-Fi, but not even the business owner would know your existence. Your privacy and security are protected at all times.
You can further take various precautionary measures before connecting to a Wi-Fi network. Some of these are listed below:
- Disable/Turn off sharing settings so no one can access your mobile device
- Use HTTPS websites whenever you use the internet
- Use a Firewall
- 2-factor authentication on all login credentials
- Turn off Wi-Fi
- After using, select ‘Forget’ on a particular Wi-Fi
Public Wi-Fi VPN – The Ultimate Solution
The important factor that protects your online activity and device is to get a Wi-Fi VPN. Nothing gives you better online protection than a VPN because it completely hides you on the internet, and no one would ever know that you exist online.
Moreover, tourists are more vulnerable targets for cybercriminals due to their frequent desire to share updates on social media, which necessitates a constant internet connection. Consequently, tourists often fall prey to cyberattacks, resulting in the theft of their valuable data. A highly recommended precautionary measure is to use a reliable traveling VPN consistently. In this regard, ExpressVPN stands out as my top recommendation.
Wi-Fi VPNs to Bypass Blocked Websites in Schools
Schools normally block social media websites such as Twitter, Facebook, Instagram, and others to prevent students from spending too much time on the internet. These limitations are enforced by school administration so that students can focus on their studies.
However, the best VPN for schools can easily bypass blocked websites in schools and let students access Facebook, Twitter, Instagram, and many social media websites. A VPN Wi-Fi hack will change your IP address and allow you to bypass geo-restrictions.
Sometimes, school Wi-Fi blocks VPN; in that case, you must confirm with the VPN provider whether it could break the blockage.
Further, when you subscribe to a VPN for school, you can unblock streaming websites such as YouTube or Netflix while also playing games by unblocking gaming websites. It makes torrenting and accessing WhatsApp easier. However, you may want to avoid the best VPN for school Wi-Fi free of cost since they may land you in hot waters due to their unreliability.
FAQs – Best VPN for Wi-Fi
Which VPN works best with Wi-Fi?
ExpressVPN stands out as the best VPN Wi-Fi. Renowned for its robust security capabilities and features, it uses AES-256 encryption, one of the most potent available, ensuring your data remains indecipherable to unauthorized viewers.
Can you use a VPN to get Wi-Fi?
Yes, a VPN can help you secure your connection when using Wi-Fi, especially public Wi-Fi. It encrypts your data and keeps your browsing activities private so you can stay safe from hackers and other online threats. However, you must connect to Wi-Fi separately before using the VPN.
Should I use a VPN on my home Wi-Fi?
Using a VPN on your home Wi-Fi is unnecessary since it is already secured. However, it is recommended to use a VPN when using unsecured public Wi-Fi networks to protect your data from being intercepted by hackers. VPNs are also useful for safeguarding online privacy from government authorities and tech giants.
Is it safe to use airport Wi-Fi without a VPN?
No, it’s not safe to use airport Wi-Fi without a VPN. Always make sure you protect yourself with a VPN, antivirus, and strong digital security before entering sensitive information over public Wi-Fi networks.
Will a VPN protect me against hackers on public Wi-Fi?
Indeed, a VPN acts as a powerful shield against unauthorized access to your data. By employing advanced encryption, it ensures that your online actions remain virtually invisible to hackers. Additionally, it conceals your true IP address, significantly reducing the risk of becoming a target in cyber attacks.
Can you use a VPN on a Wi-Fi network?
Yes, you can use a VPN on a Wi-Fi network. It’ll help you keep safe if anyone tries to snoop on your web traffic or access your device. Since your data will be encrypted, they’ll have difficulty getting through. That’s why I highly recommend ExpressVPN because its Threat Manager can detect such attacks and ward them off.
Is it better to use VPN on Wi-Fi?
Yes, it is better to use a VPN on Wi-Fi especially when using public networks. A VPN encrypts your internet traffic, making it difficult for hackers to intercept your data. This protects your online privacy and keeps your sensitive information safe.
Is it safe to use hotel Wi-Fi?
No, it’s unsafe to use hotel Wi-Fi. Hotel networks have weak security measures, which make them easy targets for cybercriminals. They could intercept your data and steal your sensitive information. It’s better to use the best VPN for hotel Wi-Fi when connecting to hotel Wi-Fi to protect your privacy and stay safe online.
Final Advice
Don’t compromise the security of your personal and financial information because, without a VPN, you are just a sitting duck for data snoopers. This is why I recommend you get a reliable VPN for your Wi-Fi connection.
ExpressVPN is my most trusted choice for this. This VPN offers the ultimate security features that keep you secure on your Wi-Fi connection, thousands of servers across the globe, and multiple simultaneous connections, which makes this provider the best VPN for Wi-Fi.
The suggested services in this article work best as either school Wi-Fi, hotel Wi-Fi VPN, or a public Wi-Fi VPN.
