
When you use a VPN, your data is routed through a proxy for added security. Yet, not all internet activities need such protection. The best VPN with split tunneling lets you choose which apps or sites send data through the VPN, like torrent clients, and which connect directly to the internet, such as banking connected via your local IP.
Also, the best VPN with this feature allows for a more refined online security approach, creating separate pathways for sensitive and regular data. This lets you choose which apps or websites use the VPN, enhancing control over your privacy. Although configuring split tunneling can be complex on some operating systems, it is much simpler with VPNs that include this feature.
Among VPNs with split tunneling, ExpressVPN shines for its ease of use and comprehensive features, ideal for Australians prioritizing security and convenience. This guide explains how to use split tunnelling VPN effectively, highlighting the importance of choosing a supportive VPN and navigating the selection process.
Quick Overview: Best VPN with Split Tunneling
Here is a brief overview of my selected best VPN with split tunneling:
ExpressVPN – Best VPN with Split Tunneling:
Offers a split tunneling option on Windows, Mac, Android, and router apps with a 30-day money-back guarantee. It is known for its various split tunneling methods, vast server network, and strong encryption.
➔ Get a special ExpressVPN offer today: $6.67/mo - Save up to 49% with exclusive 1-year plans + 3 months free!
Surfshark – Budget-friendly Split Tunneling VPN:
Highly affordable split tunneling VPN for Windows and Android. Its Bypasser tool and NoBorders mode offer robust security and flexibility for restrictive regions.
➔ Get a special Surfshark deal: $2.49/mo - Save up to 77% with exclusive 2-year plan + 30-day money-back guarantee!
NordVPN – Large Network VPN with Split Tunneling:
Offers split tunneling, Kill switch, Nordlynx, and OpenVPN protocol on Windows and Android apps. Offers split tunneling through browser extensions, with over 6000+, excellent speeds, and strict privacy policies.
➔ Get the best of NordVPN: $3.99/mo - Save up to 63% with exclusive 2-year plan + 3 months free for a friend!
CyberGhost – User-friendly VPN with Split Tunneling:
User-friendly VPN with Smart Rules for app and website-specific tunneling, dedicated for streaming and downloading. Offers dedicated servers with many features, including split tunneling on Windows and Android apps.
➔ Get the best CyberGhost deal: $2.03/mo - Save up to 84% with exclusive 2-year plans + 4 months free!
Private Internet Access – Popular VPN with Split Tunneling:
Its split tunneling feature is available on Windows, Android, Mac, and Linux. Provides a powerful split tunneling feature with a large server network and customizable security settings, except on iOS.
➔ Get the best Private Internet Access offer today: $2.11/mo .
IPVanish – Reliable VPN for Split Tunneling:
Provides dedicated split tunneling feature apps for FireOS and Android loaded with numerous other features, including WireGuard protocol, proxy network, and many server locations.
➔ Get a special IPVanish offer today: $2.99/mo - Get 3 Months Extra + Save 77% on 2-year plan.
AtlasVPN – Fastest VPN for Split Tunneling:
Comes with 10Gbps servers and unrestricted bandwidth for seamless streaming. Although its premium version seems lacking, the free version is one of the best. Offers split tunneling on Android.
➔ Get a special AtlasVPN offer today: $1.64/mo.
What is Split Tunneling, and Why Do I Need a Split Tunneling VPN?
Split tunneling lets you choose which traffic is encrypted through a VPN and which connects directly to the internet, balancing privacy with access to local services and devices. It’s particularly useful for remote work, separating work and personal browsing.
The necessity for a split tunneling VPN is underscored by the surge in cyberattacks, with global cybercrime costs predicted to reach $10.5 trillion annually by 2025. With over 75% of these attacks starting from an email, safeguarding digital communications becomes critical. Over half of consumers have faced cybercrime, with a third falling victim in the past year alone.
ExpressVPN is the best VPN for split tunneling, addressing these cyber threats effectively. It offers a seamless blend of security and convenience, allowing users to securely access global and local content. With ExpressVPN, users enjoy enhanced protection against cybercrime, efficient access to geo-restricted content, and fast, uninterrupted online experiences.
Best VPN With Split Tunneling [In-Depth Analysis]
Split tunneling is a feature provided by very few VPN services. That said, after hours of research and testing, I’ve listed the 7 best VPNs just for you. Not only that, I keep in mind other important security features that are essential for your online security.
Dig in further to get a complete analysis of the best VPN with split tunneling tested:
1. ExpressVPN – Best VPN With Split Tunneling

- Ultra-fast servers in 105 Countries
- Excellent unblocking capability for Netflix, Hulu & more
- Best-in-class encryption trusted security, and advanced protection features that block ads, trackers, and harmful sites.
- Connect up to 8 devices simultaneously
- 24/7 customer support through live chat
- 30-day money-back guarantee
ExpressVPN is the best VPN with a split tunneling feature that offers flexible configurations. You can get the ExpressVPN split tunneling feature on Android, Mac, and Windows apps by installing it onto your router. Unfortunately, for iOS and macOS 11 and later, split tunneling is not supported.
You can configure Express VPN split tunneling in three different ways:
- All apps use the VPN: This configuration is enabled by default, and it treats all your traffic equally. Use this setting if you want all your apps to use the VPN.
- Do not allow selected apps to use the VPN: This setting allows you to choose apps that you DON’T want to use.
- Only allow selected apps to use the VPN: This setting reverses the logic used by the above configuration. Here, you have to choose the apps that you DO want to be secured with ExpressVPN.
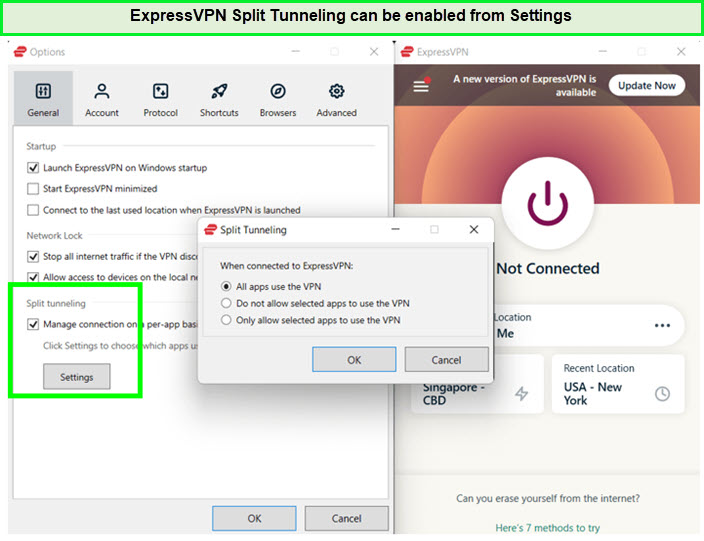
ExpressVPN Split tunneling is easily enabled in USA.
For details about the split-tunneling feature, you can check out the tutorial page on the official ExpressVPN website.
For my ExpressVPN speed test, I enabled its split tunneling feature for streaming and took a test. I recorded an average download speed of 88.78 Mbps and an upload speed of 54.22 Mbps on a 100 Mbps base connection.
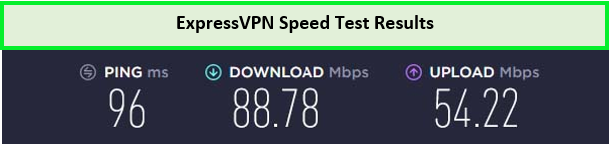
I enjoyed exceptional speeds using the ExpressVPN split tunneling option.
The 3000+ servers in 105 locations get the job done perfectly well when you want to unblock any censored websites from anywhere in the world. Furthermore, it’s high power encryption technologies also help bypass ISP throttling, allowing you to browse freely.
Besides this, ExpressVPN has excellent features for boosting the security and privacy of users, like a kill switch. It also has a Threat Manager feature that protects your device from malware attacks. It further robust security protocols like Lightway Protocol and IKEv2. These features collectively make ExpressVPN the best split tunneling VPN.
This split tunnel VPN is available for a reasonable price with a 30-day money-back guarantee. You can try it risk-free for 30 days or use ExpressVPN free trial.
Exclusive Deal
VPNRanks readers can enjoy a special ExpressVPN offer! Grab it now at $6.67/mo - Save up to 49% with exclusive 1-year plans + 3 months free
Read my complete ExpressVPN review for more details.
- Split tunneling at the router level for each device
- Include both split-include and split-exclude options on its Windows app
- Excellent speed
- 24-hour live chat customer service
- Compatible with Netflix and other streaming services
- Expensive than its competitors
2. Surfshark – Budget-friendly Split Tunneling VPN
- 3,200+ servers in 100 countries
- RAM-only servers (no hard disks)
- Unlimited simultaneous connections
- Unblocks Netflix and More
- 24/7 Customer Service
Surfshark is the most affordable VPN with a split tunneling feature, available for a budget-friendly price with a 30-day money-back guarantee. It has pretty much every nifty feature bundled in a single package that any other provider has to offer. This includes split-tunneling, which is branded by the company as Bypasser.
As the name implies, Bypasser allows you to select all apps that should use the VPNs. All the apps left unchecked in the Bypasser function will be left untouched by Surfshark VPN split tunneling, allowing these to communicate to the Internet directly.
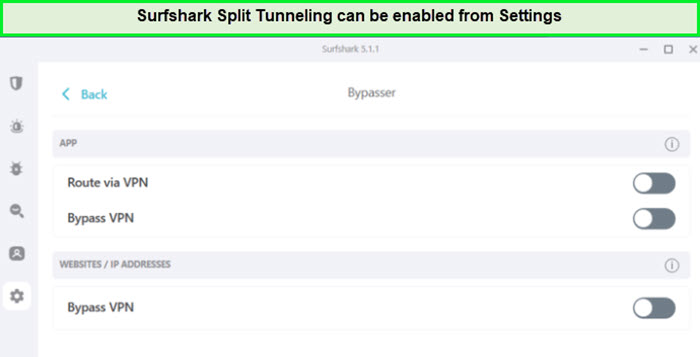
Surfshark Split Tunneling can be enabled from settings in USA.
In addition, the 3200+ servers in 100 countries are more than capable of bypassing any censored websites with ease.
Surfshark has a good logging policy and is also based in the safe jurisdiction of the British Virgin Islands. My VPN logging policy guide found Surfshark one of the only 3 VPNs with a privacy policy in the safe zone.
I conducted a Surfshark speed test after enabling the split tunneling feature. I recorded a great download speed of 81.32 Mbps and an upload speed of 76.12 Mbps on a 100 Mbps connection.
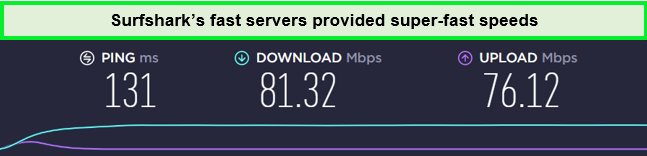
Surfshark servers were fast and efficient in unblocking restricted streaming videos in USA.
The service has built-in features like MultiHop, CleanWeb, Bypasser, AES-256-GCM encryption, and DNS leak protection. You can browse privately using Camouflage Mode.
With a single Surfshark subscription, you can connect as many devices as you want, as it supports unlimited simultaneous connections. There are apps for Windows, macOS, Android, and more.
The service is available at a very affordable price. Still, if you want to try it out for free, consider opting for the Surfshark free trial.
Exclusive Deal
VPNRanks readers can enjoy a special Surfshark offer! Grab it now at $2.49/mo - Save up to 77% with exclusive 2-year plan + 30-day money-back guarantee
To find out more about this service, explore my Surfshark review.
- Split your traffic at a low price
- Unlimited device connections
- Offers strong encryption
- Unblock all the major streaming platforms
- Server speeds fluctuate a little
- Limited server network
3. NordVPN – Secure VPN With Split Tunneling
- 6000 servers in 60 countries
- WireGuard protocol (NordLynx)
- 6 Simultaneous Connection
- DoubleVPN
- 24/7/365 Live Chat Support
- 30 Days Money Back Guarantee
NordVPN is probably the most secure VPN with a split tunneling feature. It offers a split-tunneling feature in its Android and Windows apps only.
Speaking of this feature, NordVPN’s split-tunneling works on the exclusion principle. When you enable this feature, the apps you select will be routed directly through your ISP, while the apps left unchecked will stay on the VPN tunnel. This feature works flawlessly with all compatible platforms except iOS.
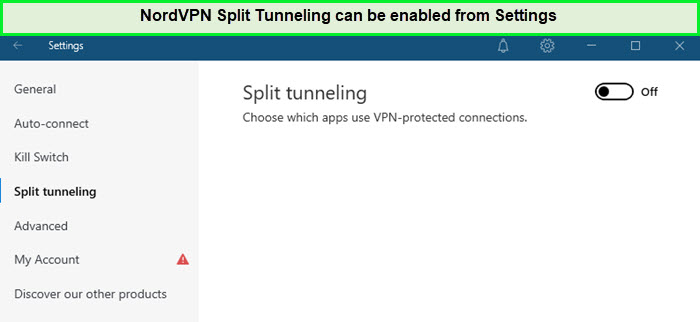
NordVPN Split Tunneling can be enabled from settings in USA.
NordVPN offers a server network of 6000+ servers in 61 countries. Its apps are available for multiple platforms, and you can simultaneously connect up to six devices.
Moreover, my NordVPN speed tests were so fine when I used its split tunneling feature during remote work. I experienced an average download speed of 83.82 Mbps and an upload speed of 44.64 Mbps for uninterrupted streaming.
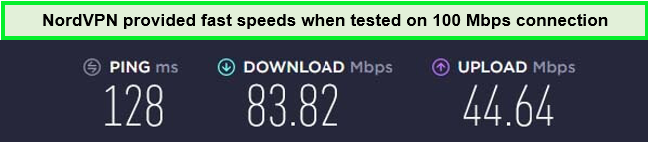
NordVPN speed results after turning on the split tunneling option in USA.
Apart from this, NordVPN offers Obfuscated servers and advanced security features such as AES-256-GCM encryption, Onion Over VPN, and the kill switch. NordVPN also offers a Double VPN technology that gives you additional security by routing the traffic through multiple VPN servers.
In case you ever find your NordVPN split tunneling not working, you can reach out to their 24/7 live chat support team to obtain immediate assistance.
You can get NordVPN for a very reasonable cost, and it comes with a 30-day money-back guarantee on all premium plans. You can also try the NordVPN free trial to check out its split tunneling feature, free of charge.
Exclusive Deal
VPNRanks readers can enjoy a special NordVPN offer! Grab it now at $3.99/mo - Save up to 63% with exclusive 2-year plan + 3 months free for a friend
To find out more about this service, explore my NordVPN review.
- Cover your browser traffic using the split tunneling
- Fair speeds
- Compatible with US Netflix and other streaming services
- High-level security features
- Best VPN tunnel via NordLynx
- The server connection can be slow at times
4. CyberGhost – User-friendly VPN With Split Tunneling
- 11651 Servers Servers in 100 Countries
- 7 Simultaneous Logins
- 45 Days Money-Back Guarantee
- Strict No Logs Policy
- 24/7 Live Chat Support
- Strong Protocols & Encryption
CyberGhost is a user-friendly VPN that supports split-tunneling functionality. Like most other VPNs, CyberGhost split-tunneling works by creating a list of apps that you want to secure.
You can easily enable the CyberGhost split tunneling feature on the Android app and Windows as well. For Windows app, it offers an exception feature that works as a Split tunnel.
All the apps excluded from this list will remain outside the VPN tunnel. You can even exclude websites by adding their URL in the exception menu. If you ever need more help enabling split tunneling on this VPN, you can approach CyberGhost Support for a clear idea.
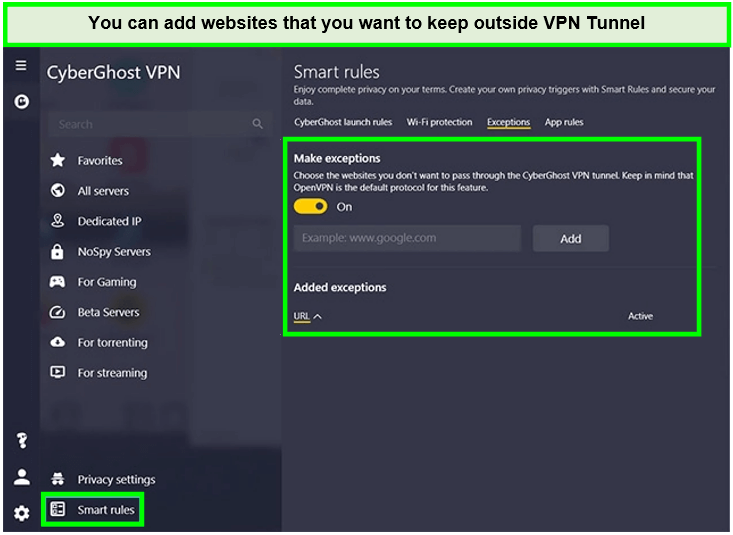
On the Windows app, the option “Exception” works as split tunneling in USA.
CyberGhost offers 11651+ servers in 100 countries, and its apps have a user-friendly interface that even a beginner can use. There is also a section with dedicated servers for streaming, torrenting, gaming, and NoSpy servers for security.
During the CyberGhost speed test on a 100 Mbps connection, I recorded a decent download speed of 75.47 Mbps and an upload speed of 69.34 Mbps.
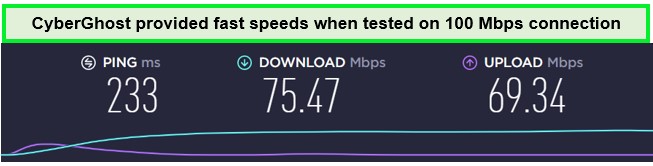
Cyberghost speed on a 100 Mbps connection when split tunneling was activated in USA.
Along with the well-functioning split-tunneling feature, CyberGhost offers various security protocols such as OpenVPN (TCP / UDP), IKEv2, and L2TP/IPSec. CyberGhost also uses AES 256-bit encryption, with SHA384 hash authentication and RSA-4096 key encryption.
It is compatible with all major devices, including Windows, Android, iOS, macOS, browsers (Chrome, Firefox), and more. It also supports 7 multi-logins so that you can secure multiple devices simultaneously.
CyberGhost is available for a very affordable price and offers an extensive 45-day money-back guarantee. You can even try the VPN out for free by using the CyberGhost free trial, and for any query, you can also reach out to its 24/7 customer support.
Exclusive Deal
VPNRanks readers can enjoy a special CyberGhost offer! Grab it now at $2.03/mo - Save up to 84% with exclusive 2-year plans + 4 months free
Find out more about this VPN in my in-depth CyberGhost review.
- Offers feature Website split-exclude and app split-include
- Rapid and trustworthy service
- No-Logs policy
- Dedicated servers for streaming
- Not suitable to use in China
- Doesn’t offer split tunneling on iOS
5. Private Internet Access – Popular VPN With Split Tunneling

- Does Not Keep Any Logs
- 24/7 Customer Support
- 7 Days Money Back Guarantee
- 35000+ Servers in 84 Countries
- SOCKS 5 proxy
- Compatible with Leading Devices
Private Internet Access is a popular VPN that packs an excellent split tunneling feature. PIA’s split tunneling feature is built directly into its apps and allows users to select which apps should be using the VPN tunnel and which should directly access the internet.
PIA has more than 35000+ servers in 84 countries. You can find the split tunneling feature under the Network tab in Settings. One of the most distinguishing features of PIA is its large server network.
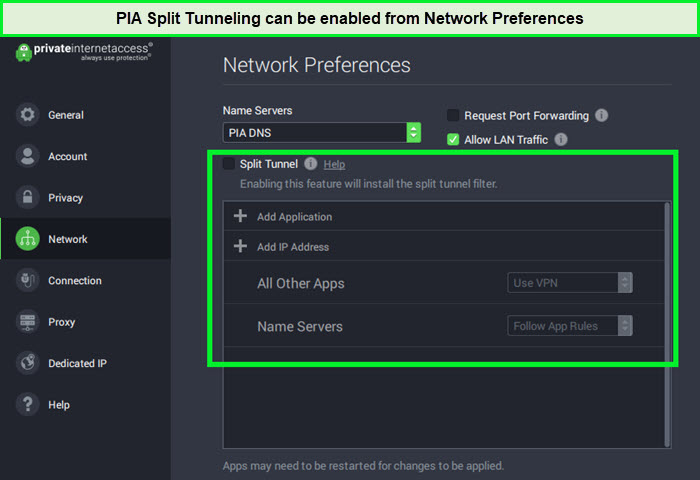
PIA Split Tunneling works easily on most of its applications in USA.
Despite being compatible with iOS, PIA doesn’t support split tunneling in any Apple device. However, you can use this feature on all desktop devices, including macOS, Linux, Windows, and more. Split tunneling is also available in Android applications under “Per Settings.”
My PIA speed test was not as impressive as other VPNs in this guide, but I recorded a fair download speed of 65.78 Mbps and an upload speed of 57.16 Mbps on a 100 Mbps connection.
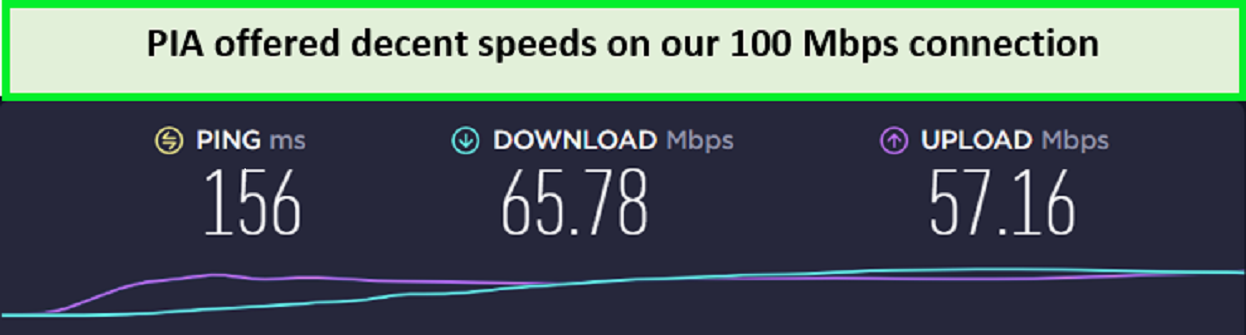
PIA speed test on a 100 Mbps connection using split tunneling feature in USA.
Aside from split tunneling, PIA offers powerful features like a secure kill switch and IP/DNS leak protection. You can choose from AES 128-bit and AES 256-bit encryption, although 256-bit is recommended as it offers better security. It also offers a Built-in ad-blocking feature called MACE, which blocks ads and malware.
PIA is headquartered in the USA (a major member of the 5/9/14 Eyes alliance). However, the provider offers a strict no-logs policy, and it is safe to use. PIA does not log identifiable user data, so you are safe with this provider.
If I talk about pricing, PIA is quite affordable. It also gives its users the freedom to secure 10 simultaneous connections and offers a free trial and a full 30-day money-back guarantee.
Exclusive Deal
VPNRanks readers can enjoy a special PIA offer! Grab it now at $2.11/mo
To find out more about this service, explore my PIA review.
- Quite affordable for the security features it provides
- Thousands of servers spread all over the world
- Audited Zero-log policy
- Split tunneling is available on all desktop devices
- 24/7 Customer Support
- Not quite as quick as ExpressVPN
- Split tunneling is not available on smartphones
- US-based VPN provider
6. IPVanish – Reliable VPN With Split Tunneling

- PPTP, L2TP/IPSec & OpenVPN protocols
- 40,000+ IPs & 1000+ servers in 60+ countries
- 10 Multi logins
- 7-Day Money Back Guarantee
- 256bit AES encryption
IPVanish is a reliable VPN with split tunneling. This feature makes it a perfect choice for families or individuals with numerous devices, ensuring everyone can enjoy unrestricted streaming.
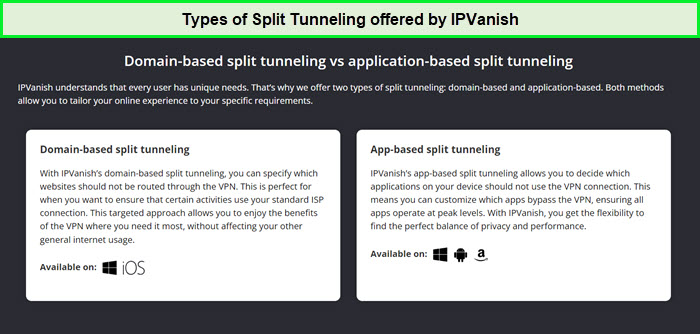
IPVanish’s split tunneling feature allows users to route app or domain-based traffic outside the VPN tunnel selectively. Compatible with Windows, Android, iOS, and Amazon Fire TV, users can enable this feature through the app’s settings.
By navigating to Split Tunneling settings, you can choose which apps or URLs bypass the VPN, connecting directly via your ISP. This ensures specific applications do not use the VPN connection while all other traffic remains encrypted through the VPN tunnel.
The IPVanish Split Tunneling feature works on most of its available apps in USA.
The speed performance of IPVanish is noteworthy. In my IPVanish speed test, it clocked in at a download speed of 70.05 Mbps and an upload speed of 32.15 Mbps on a 100 Mbps connection, ensuring smooth, bufferless streaming. The consistent speeds across its servers particularly impressed me.
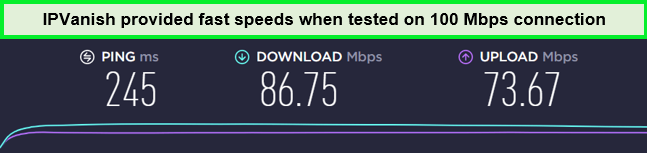
IPVanish offers fast speeds while.
IPVanish boasts an extensive network of 2200 servers in 75 countries.
Compatibility is another forte of IPVanish. It seamlessly integrates with various devices and operating systems, including Android, iOS, Mac, and Windows. I could install IPVanish on Kodi, as well as Firestick, Smart TV, and Roku without much trouble and, in return, got the ability to stream across various devices.
In terms of security, IPVanish doesn’t disappoint. It provides military-grade AES 256-bit encryption, split tunneling, and robust DNS leak protection, combining optimal security with the capability to access geo-blocked content.
Considering its reliability and features, IPVanish’s pricing is a steal. With a 30-day money-back guarantee and an IPVanish free trial, coupled with responsive live chat support, this VPN solidifies its position as a user-friendly and dependable streaming VPN.
Exclusive Deal
VPNRanks readers can enjoy a special IPVanish offer! Grab it now at $2.99/mo - Get 3 Months Extra + Save 77% on 2-year plan.
Learn more about this VPN through the VPNRanks IPVanish review.
- Offers efficient streaming on Netflix, Hulu, Amazon Prime, and more
- Equips security features that are quite robust
- Unlimited simultaneous connections
- Slow speeds on international servers
- Live chat isn’t reliable
7. AtlasVPN – Fastest VPN With Split Tunneling

- 3 servers in 2 countries (US and Netherlands).
- Offers unlimited bandwidth.
- Works with Netflix, Hulu, Amazon Prime, and BBC iPlayer.
- Top downloading speed of 32 Mbps on a 100 Mbps connection.
- 1 device connection.
AtlasVPN is a fast VPN with split tunneling. With a robust server network that covers a multitude of countries, AtlasVPN ensures that geographical boundaries don’t limit your speeds while using its split tunneling feature.
The primary reason to opt for AtlasVPN is its impressive 10Gbps server speeds, which are crucial for streaming content in high definition without buffering issues. By using state-of-the-art server technology, AtlasVPN provides reliable and fast connections that make it an excellent choice for split tunneling.
Atlas VPN’s split tunneling feature currently only works on its Android app. This is done through the app’s settings, where you can access split tunneling options and choose the apps you prefer not to route through the VPN.
Once selected, these apps will use a direct ISP connection, ensuring that only desired traffic benefits from VPN protection. This feature enhances user control over network traffic, optimizing security and performance.
Atlas VPN Split Tunneling works on its Android app in USA
AtlasVPN boasts a server strength of 1000+ servers in 42 countries, including 12. This means you can watch your favorite geo-restricted shows at the same time as your local apps without experiencing lag or quality drops.
Furthermore, Atlas VPN provides streaming-optimized servers, ensuring you have the best possible experience. In my Atlas VPN speed test, it clocked a fast download speed of 83.98 Mbps, whereas the uploaded speed was 41.64 Mbps.
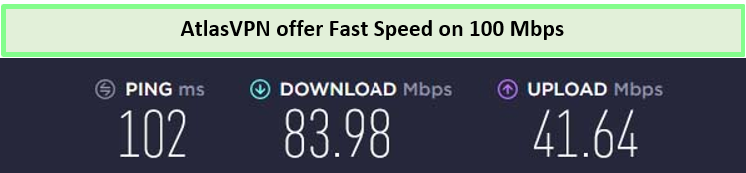
The speeds of AtlasVPN were quite reliable after using Splt Tunneling
Atlas VPN has Windows, Mac, Android, iOS, and Linux apps. It, like Surfshark, allows users to connect to unlimited devices simultaneously.
AtlasVPN doesn’t compromise on security, either. It provides powerful encryption and privacy features like virus and ad-free browsing with SafeBrowse, an IP rotator, and data breach monitoring to keep your streaming habits confidential.
It is a freemium VPN service, which means if you want all of the features, you’ll have to buy the full AtlasVPN subscription
Exclusive Deal
VPNRanks readers can enjoy a special AtlasVPN offer! Grab it now at USD 1.70/mo (3 years + 3 months extra, save 85%).
- Affordable subscription tiers
- Unblock VoD services
- Auto-connect and quick-connect options
- Unlimited simultaneous connections.
- The data district and confidentiality are not clear.
- Split Tunneling works on Android only.
Comparison Table – Split Tunneling VPN
Here is a comparison table that shows all the most essential details of the best Split Tunneling VPN:
| VPNs |  |
||||||
|---|---|---|---|---|---|---|---|
| Split Tunneling Reliability | 1 | 2 | 3 | 4 | 5 | 6 | 7 |
| Compatible Devices | Android, iOS, Windows, Mac, & more | iOS, Android, Windows, Roku, etc | Windows, iOS, Android, Firestick, Roku, etc | Android, Windows, macOS, & iOS | Windows, Android, iOS, Apple TV | Mac, Windows, Android, & Fire TV | Windows, Mac, Android, iOS, & Linux |
| Speed on 100 Mbps | 88.78 Mbps Mbps | 81.32 Mbps | 83.82 Mbps | 75.47 Mbps | 65.78 Mbps | 86.75 Mbps | 83.98 Mbps |
| Simultaneous Connections | 8 Devices | Unlimited Devices | 6 Devices | 7 Devices | 10 Devices | Unlimited Devices | Unlimited Devices |
| Lowest Price | $6.67/mo | $2.49/mo | $3.99/mo | $2.03/mo | $2.11/mo | $2.99/mo | $1.70/mo |
Split Tunneling VPN – Testing Methodology
I took a comprehensive approach to evaluate split tunneling VPNs. My assessments were based on expert analysis, real-world experience, and rigorous performance and security tests. When testing split tunneling VPNs, I focused on the following key aspects:
- Split Tunneling Support: I prioritized VPNs that provide split tunneling functionality across all their applications. This ensured that users could choose which traffic goes through the VPN and which accesses the regular internet connection.
- Speed: I measured download speeds on connections to VPN servers located worldwide. A reliable split tunneling VPN should offer fast and consistent speeds to maintain seamless internet activities.
- Security: Implementing split tunneling can potentially introduce security risks if not done properly. Therefore, I thoroughly assessed VPNs for robust encryption protocols and ensured they were free of data leaks.
- Streaming: I conducted real-world tests to determine which VPNs can consistently access popular streaming services. A good split tunneling VPN should enable users to access geo-restricted content without compromising speed or performance.
- Customer Support: I interacted with each VPN’s customer support staff as secret shoppers to assess response times and service quality. Efficient and helpful customer support is crucial for a positive user experience.
- Privacy: Privacy is paramount in my evaluations. I meticulously inspected each VPN provider’s privacy policy and terms of use to ensure they adhere to a strict no-logs policy, safeguarding users’ online activities.
- Value for Money: I favored VPNs that offer excellent value, providing robust features and performance at reasonable prices. Transparency in billing practices is also essential to gain my recommendation.
Through these thorough assessments, I provide reliable recommendations for split tunneling VPNs, enabling users to make informed decisions for their online privacy and security needs.
Benefits of VPN Split Tunneling
A split tunneling VPN gives the benefit of securing online activity while facilitating quick internet access. Let’s take a look at the other benefits you can avail of by using one of the best split tunneling VPN providers:
- Conserve Bandwidth: Split tunneling helps save bandwidth by allowing you to choose which data or applications pass through the VPN tunnel while the rest access the internet directly. This optimization leads to improved internet speeds and network performance.
- Secure Connection for Remote Workers: With split tunneling, remote workers can securely access their company’s network from unsecured environments. Sensitive work-related traffic goes through the VPN, while non-business traffic uses the local connection, ensuring privacy and productivity.
- Work on a Local-Area-Network (LAN): Split tunneling allows you to access local resources, such as printers, through your LAN, while still benefiting from VPN security.
- Stream Content Without Foreign IP Addresses: Enable split tunneling to stream geo-restricted content without relying on foreign IP addresses. This feature is particularly useful for accessing streaming platforms with better performance and more available content through a local IP address.
- Speed up your connection: Split tunneling enables your VPN to process data faster because you aren’t tunneling all of your traffic through a single tunnel.
- Allows greater Control: Split tunneling lets you choose which website traffic or data should traverse via your VPN and which should not.
- Bypass Restrictions: Split tunneling enables you to use your VPN to access geo-restricted websites and streaming content while using your local internet connection to access local services. By turning on the split tunneling feature, you can make the most of search engines and websites that function best when they know your location.
How Do You Set Up a Split Tunnel?
Follow these simple steps to activate split tunneling on your device:
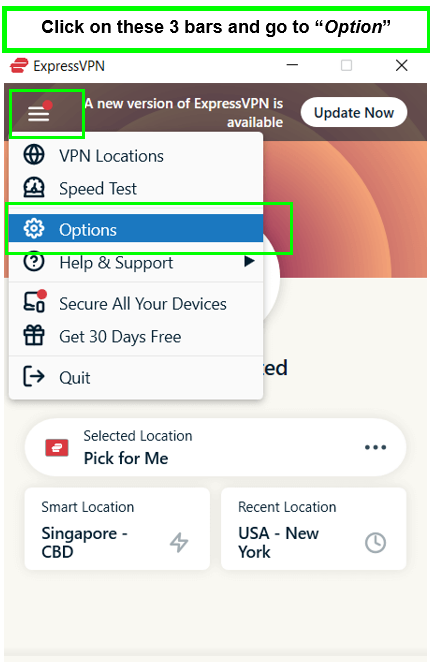
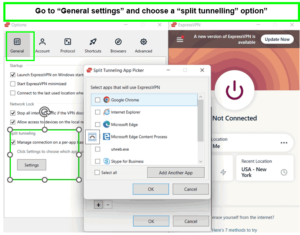
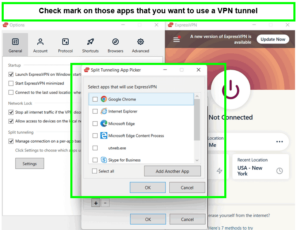
- Open the VPN’s Settings or Menu, and go to “Options.” I am using ExpressVPN to show you this setup.

- From the general setting, you should be able to manage your VPN split tunneling configuration on a specific app or URL basis.

- Following that, you can decide which apps use the VPN and leave those unchecked that run on an open network

- Here you go! You can now manage your device traffic through split tunneling.
How to Use a Split Tunneling VPN?
Using a split tunneling VPN is straightforward on most VPNs. Here is a general guide to enabling split tunneling on VPN:
- Launch your VPN app and go to settings/preferences.
- Enable split tunneling within the app.
- Choose to exclude specific apps from the VPN or include only certain ones.
- Add apps or websites you want to bypass the VPN or use exclusively.
- Connect to your VPN server to activate split tunneling.
- This allows secure VPN use for sensitive tasks while maintaining full speed or local access for others.
By selecting which apps to protect, you can enjoy secure VPN connections for sensitive activities and a direct connection for tasks requiring full speed or local access through the best tunnel VPN. Remember that the exact steps vary based on your VPN provider and platform.
Should I Use Split Tunneling on VPN?
Yes, you should use VPN split tunneling if you prioritize protecting sensitive data while maintaining faster internet speeds. If you are comfortable segregating your online activities, using a VPN split tunneling can be a suitable option for you.
To secure your important data without slowing down your internet, you should use a VPN split tunneling. For example, if you have high-end security software installed on your PC that offers the same security protections as your firm, you do not need to use VPN split tunneling.
But if you do not have such software, you must use VPN split tunneling for traffic headed to the server of your company.
Moreover, a split tunneling VPN may be a good option if you’re happy to divide your online activity into activities you want to keep private and ones you think do not need much protection.
Pros and Cons of Split Tunneling
As with any other technology, split tunneling too, has its pros and cons:
Advantages:
- Simultaneous Use: With split tunneling, you can use both a direct internet connection and a VPN connection at the same time, allowing you to choose which traffic passes through the VPN tunnel and which doesn’t.
- Bandwidth Conservation: Split tunneling helps conserve VPN bandwidth by routing only specific data or applications through the VPN, improving overall internet speeds.
- Local Network Access: You can access your local network, including devices like printers and smart home devices, even while using the VPN.
- Latency Optimization: Non-VPN apps and devices won’t suffer from increased latency, ensuring smooth performance.
- Selective Traffic Routing: You can choose which traffic passes through the VPN tunnel, enhancing privacy for sensitive activities.
- Access to Local and Foreign Content: Enjoy local network access and reach geographically restricted content without compromising speed or security using a split tunneling VPN.
- Improved Speed and Performance: Avoid overloading the VPN with unnecessary traffic for better internet speeds for certain applications.
- Maintain Online Functionality: Keep using services like banking apps that may not operate well with a VPN by bypassing the VPN where necessary.
Disadvantages:
- Security Concerns: The main drawback of split tunneling is potential security risks. Improper configuration could create a backdoor for attackers to infiltrate VPN-protected connections through the device’s non-VPN connection. However, when configured correctly, split tunneling remains safe for most users.
- Complex Configuration: Configuring split tunneling can be complicated for those unfamiliar with VPN settings.
- Inconsistent Protection: Not all internet traffic is encrypted, which can lead to privacy inconsistencies.
- Risk of Data Leaks: Incorrect configuration could expose your data, especially if the VPN connection drops unexpectedly.
- Company Compliance Issues: For remote workers, split tunneling might violate company security policies if sensitive data is not routed through the VPN.
Types of Split Tunneling With VPN Services
Different VPN providers offer varying implementations of split tunneling, each designed to cater to specific user needs:
App-Based Split Tunneling
This common form allows you to select specific apps to bypass the VPN, which is ideal for those needing direct internet access for optimal performance. ExpressVPN and Surfshark are examples of providers that offer this feature.
Inverse Split Tunneling
Inverse split tunneling lets you specify which apps should use the VPN by default while all others connect directly to the internet, which is useful for ensuring that only select applications have their data encrypted. Providers like NordVPN and CyberGhost offer this functionality.
URL-Based Split Tunneling
Some VPNs offer this through browser extensions, allowing you to choose websites that bypass the VPN, which is beneficial when accessing local versions of websites or when certain sites block VPN connections. Private Internet Access is known for its flexible split-tunneling options.
Understanding these types can help you choose the best VPNs for split tunneling based on your specific needs.
Can I Use a Free VPN for Split Tunneling?
Yes, you can use a free VPN with split tunneling, but it is important to understand that split tunneling VPN free services may not always provide the best experience. Generally, free VPNs have limitations that could affect your split tunneling experience.
They often lack the robust security features and are less likely to offer the split tunneling feature. Another significant concern with free VPNs is privacy. Some free services may track and sell user data to third parties as a means of generating revenue, defeating the purpose of using a VPN. In contrast, premium VPNs often adhere to strict no-logs policies, ensuring that your activities remain private.
When it comes to split tunneling with a VPN, the best option is to invest in a premium VPN service. Paid VPNs are more likely to offer advanced split tunneling features, enabling you to enjoy the flexibility of choosing which apps use the VPN and which don’t. They also provide better security, faster speeds, and more reliable connections—essential for a good split tunneling VPN experience.
Other Valuable VPN Guides by VPNranks
- Best VPN for iPad: Say goodbye to censorship & restrictions.
- Best VPN for OpenVPN: Find the right OpenVPN client.
- Best VPN for Mac: Experience the best of online privacy and security on your Mac.
- Best VPN for Windows: Ensure top-tier security and privacy for your Windows PC.
- Best VPN for Kodi: Keep your Kodi activities anonymous and secure with a VPN.
- Best VPN for Crypto Trading: Experience uninterrupted trading with a fast and reliable VPN service tailored for crypto enthusiasts.
FAQs – Best VPN With Split Tunneling
Which VPN supports split tunneling?
ExpressVPN supports split tunneling on Android, Mac, routers, and Windows, enabling users to choose which apps go through the VPN and which connect directly to the internet. Detailed setup guides and troubleshooting tips are available, including instructions for enabling split tunneling in the app’s “VPN connection” settings.
Does NordVPN allow split tunneling?
Yes, NordVPN allows split tunneling. It is available on Windows 7 and 8.1, Windows 10 and 11, Android, and Android TV, making it useful for scenarios where a VPN connection may not be necessary, such as when using trusted applications.
Is split tunneling a VPN feature?
Yes, split tunneling is a feature of virtual private networks (VPNs). It enables you to direct some of your application or device traffic through an encrypted VPN while allowing other applications or devices to access the internet directly.
Does CyberGhost support split tunneling?
CyberGhost supports split tunneling, but only on its Android app. While it may lack split tunneling across all platforms, a common feature among other VPN providers, CyberGhost offers the option to whitelist specific websites with its VPN service.
What is VPN split tunneling?
VPN split tunneling is a feature that allows you to selectively route some of your application or device traffic through an encrypted VPN connection, while letting other applications or devices connect directly to the internet without VPN encryption.
Is it safe to use split tunneling?
Utilizing split tunneling effectively can enhance your privacy. Instead of disabling your VPN entirely, you can selectively route certain apps and websites through the VPN for protection, while allowing others to bypass it, optimizing your online experience.
Does split tunneling slow down internet?
No, split tunneling does not slow down the internet. Instead, it typically enhances internet speeds for traffic that doesn’t go through the VPN.
This is because it allows certain data to directly access the internet, reducing the load on the VPN server and avoiding the latency that encryption can introduce, resulting in quicker connection speeds for that data.
Does split tunneling add latency?
No, split tunneling does not add latency; rather, it can improve latency and optimize bandwidth by reducing the load on the VPN server. This is achieved by routing low-risk traffic, such as video streaming, directly to the internet instead of through the dedicated VPN gateway, especially in scenarios where the gateway handles a significant amount of traffic.
Which VPN client does split tunneling without issues?
For split-tunneling without a hitch, ExpressVPN stands out. With its user-friendly interface and robust security measures, ExpressVPN seamlessly integrates split-tunneling functionality, allowing you to tailor your VPN usage to specific apps and websites while maintaining optimal performance and privacy.
Is VPN split tunneling good or bad?
Split tunneling in VPNs has its pros and cons. On one hand, it provides flexibility, optimizing performance by selectively routing traffic through the VPN. However, on the downside, it can expose non-VPN traffic to potential security risks, compromising both data and the entire user network.
How do I know if my VPN is split tunneling?
Testing your VPN split tunneling is effectively done by trying out the URLs or apps you’ve selected to determine if they pass through the VPN. This can be achieved by verifying access to region-restricted content or checking your IP address to ensure it reflects the VPN connection.
What is inverse split tunneling?
Inverse split tunneling specifies which apps or devices are protected by the VPN, with all others excluded by default, contrasting with normal split tunneling that protects everything except explicitly excluded items. It’s akin to using a whitelist (inverse split tunneling) versus a blacklist (normal split tunneling) for VPN connections, focusing on specific apps, devices, websites, or ports for VPN use or exclusion.
What is split tunneling on VPN?
Split tunneling on a VPN enables simultaneous routing of internet traffic through both a VPN and a local network connection. This approach allows for the encryption of data while optimizing bandwidth usage. It’s a networking technique that permits a user to access different security domains, such as a public network and a local or wide area network, concurrently through the same or separate network connections.
Does OpenVPN have split tunneling?
Yes, OpenVPN does support split tunneling, although not every VPN service utilizing OpenVPN may offer this feature.
Final Thoughts
As the guide for the best VPN with split tunneling ends, I hope that you got the idea of what VPN split tunneling is, how a split tunneling VPN works, and whether to use it or not.
For your ease, I have tested this split tunneling feature on all of the 7 best VPNs. However, it’s impossible to pick the best one. Still, if you ask, I recommend you install ExpressVPN if you don’t want to compromise on your speed connections..
So make the most of the VPN split tunneling and make your online activities secure and your online streaming fast!








I’m looking for split-tunneling that allows traffic to my company network to go through my companies VPN tunnel and all other traffic to go through the VPN service. I believe that this requires IP-based routing. I haven’t been able to find a VPN service that supports the scenario. I would think that many people would need such an option. I would be interested to learn what VPN services would allow the above scenario.
Hello,
Unfortunately, what you are looking for isn’t achievable with the VPN providers on our list.
You require an IKEV or IPSec VPN tunnel created between two endpoints is referenced by a route that determines which traffic is sent through the tunnel based on a destination IP address.
Thank you for your response.